deer
1
版本:开源版本 emqx5.8.9
系统:ubuntu22
psk 配置:
EMQX.conf:
psk_authentication {
enable = true
separator = “:”
init_file = “/opt/emqx5/etc/psk_file.txt”
}
include “listeners_psk.conf”
#listeners_psk.conf 配置:
listeners.ssl.default {
bind = “0.0.0.0:2065”
enable = true
ssl_options {
#versions = [“tlsv1.2”]
versions = [“tlsv1.2”, “tlsv1.1”, “tlsv1”]
ciphers = “PSK-AES128-GCM-SHA256,PSK-AES256-GCM-SHA384,PSK-AES128-CBC-SHA,PSK-AES256-CBC-SHA”
verify = verify_none
fail_if_no_peer_cert = false
}
}
#测试代码
mosquitto_pub -h 127.0.0.1 -p 2065
-t iot_v_device_test/FD12356/message
-m “test message”
–psk-identity psk-device
–psk b865523d4db1a06aa2c8ac07d605d789
–tls-version tlsv1.2
–insecure
#psk_file:txt:
psk-device:b865523d4db1a06aa2c8ac07d605d789
#报错信息:
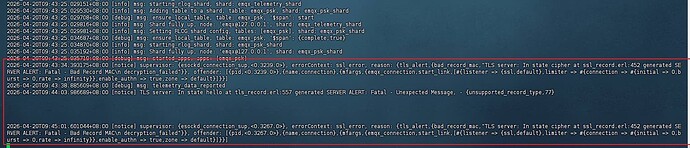
2026-04-18T12:46:52.611295+08:00 [notice] supervisor: {esockd_connection_sup,<0.3400.0>}, errorContext: ssl_error, reason: {tls_alert,{bad_record_mac,“TLS server: In state cipher at ssl_record.erl:452 generated SERVER ALERT: Fatal - Bad Record MAC\n decryption_failed”}}, offender: [{pid,<0.3400.0>},{name,connection},{mfargs,{emqx_connection,start_link,[#{listener => {ssl,default},limiter => #{connection => #{initial => 0,burst => 0,rate => infinity}},enable_authn => true,zone => default}]}}]
根据官网资料配置的,哪位大佬知道啥问题
这是 TLS-PSK 套件和配置格式不匹配导致的,你先按官方示例改一版最小可用配置再测。
你这份配置里有几个问题:
- 用了全角引号
“ ” 和长横线 –,配置文件/命令行都应该用 ASCII:" 和 --
- PSK 套件建议先用文档里的
RSA-PSK-* 组合,不要先混 PSK-*
- PSK 密钥长度要和套件匹配(比如 AES128 对应 128 bit)
先用这版(关键是 versions + ciphers):
psk_authentication {
enable = true
separator = ":"
init_file = "/opt/emqx5/etc/psk_file.txt"
}
listeners.ssl.default {
bind = "0.0.0.0:2065"
enable = true
ssl_options {
versions = ["tlsv1.2", "tlsv1.1", "tlsv1"]
ciphers = [
"RSA-PSK-AES256-GCM-SHA384",
"RSA-PSK-AES256-CBC-SHA384",
"RSA-PSK-AES128-GCM-SHA256",
"RSA-PSK-AES128-CBC-SHA256",
"RSA-PSK-AES256-CBC-SHA",
"RSA-PSK-AES128-CBC-SHA"
]
verify = verify_none
fail_if_no_peer_cert = false
}
}
psk_file.txt 按这个格式:
emqx_c:BA0DB2A3448345A3A13A91C2ADA44778
测试命令也改成 ASCII 参数:
mosquitto_pub -h 127.0.0.1 -p 2065 \
-t iot_v_device_test/FD12356/message \
-m "test message" \
--psk-identity emqx_c \
--psk BA0DB2A3448345A3A13A91C2ADA44778 \
--tls-version tlsv1.2 \
--insecure -d
如果还报 bad_record_mac,贴两段输出:
mosquitto_pub ... -d 全量输出openssl ciphers -v 'RSA-PSK' 输出(确认客户端 OpenSSL 真支持这些套件)
deer
3
首先感谢您的回复
emqx.conf 配置:
psk_authentication {
enable = true
separator = “:”
init_file = “/opt/emqx5/etc/psk_file.txt”
}
include “listeners_psk.conf”
listeners_psk.conf
listeners.ssl.default {
bind = “0.0.0.0:2065”
enable = true
ssl_options {
versions = [“tlsv1.2”, “tlsv1.1”, “tlsv1”]
ciphers = [
“RSA-PSK-AES256-GCM-SHA384”,
“RSA-PSK-AES256-CBC-SHA384”,
“RSA-PSK-AES128-GCM-SHA256”,
“RSA-PSK-AES128-CBC-SHA256”,
“RSA-PSK-AES256-CBC-SHA”,
“RSA-PSK-AES128-CBC-SHA”
]
verify = verify_none
fail_if_no_peer_cert = false
}
}
psk_file.txt
emqx_c:BA0DB2A3448345A3A13A91C2ADA44778
测试代码:
log
另外:我用 stunnel 做为psk 认证 测试是可以的;设备也能正常连接
那 mosquitto 里应该转成 hex-decoded,看下面这个回答
1 个赞
deer
5
非常感谢,按着您说的这种 ASCII HEX 是可以的(每个字符转 HEX),多谢!